Adding an Amazon S3 Source
An Amazon S3 Source connects to an existing Amazon S3 bucket. Imgix connects using the credentials you supply, so assets don’t have to be public.
Setting Up Your S3 Source
Note: When retrieving S3 objects from the us-east-1 region, Imgix uses the s3-external-1.amazonaws.com hostname to retrieve assets whenever possible to ensure read-after-write consistency, and will fall back to the default hostname of s3.amazonaws.com if necessary.
-
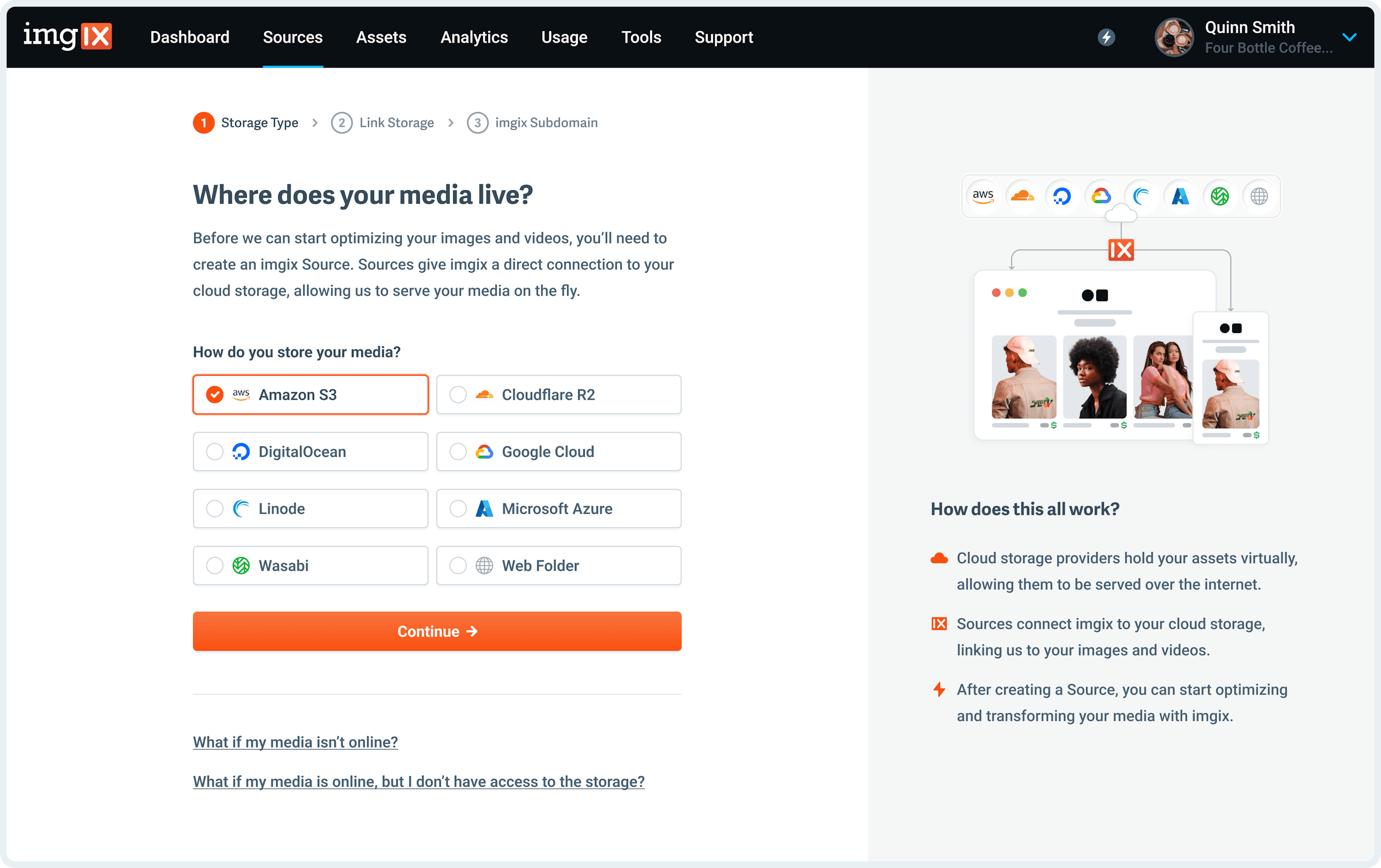
Go to the Sources page in the Imgix dashboard and click the New Source button.
-
Select Amazon S3 from the How do you store your media? radio options.
-
Fill in the details for your Amazon S3 Source.
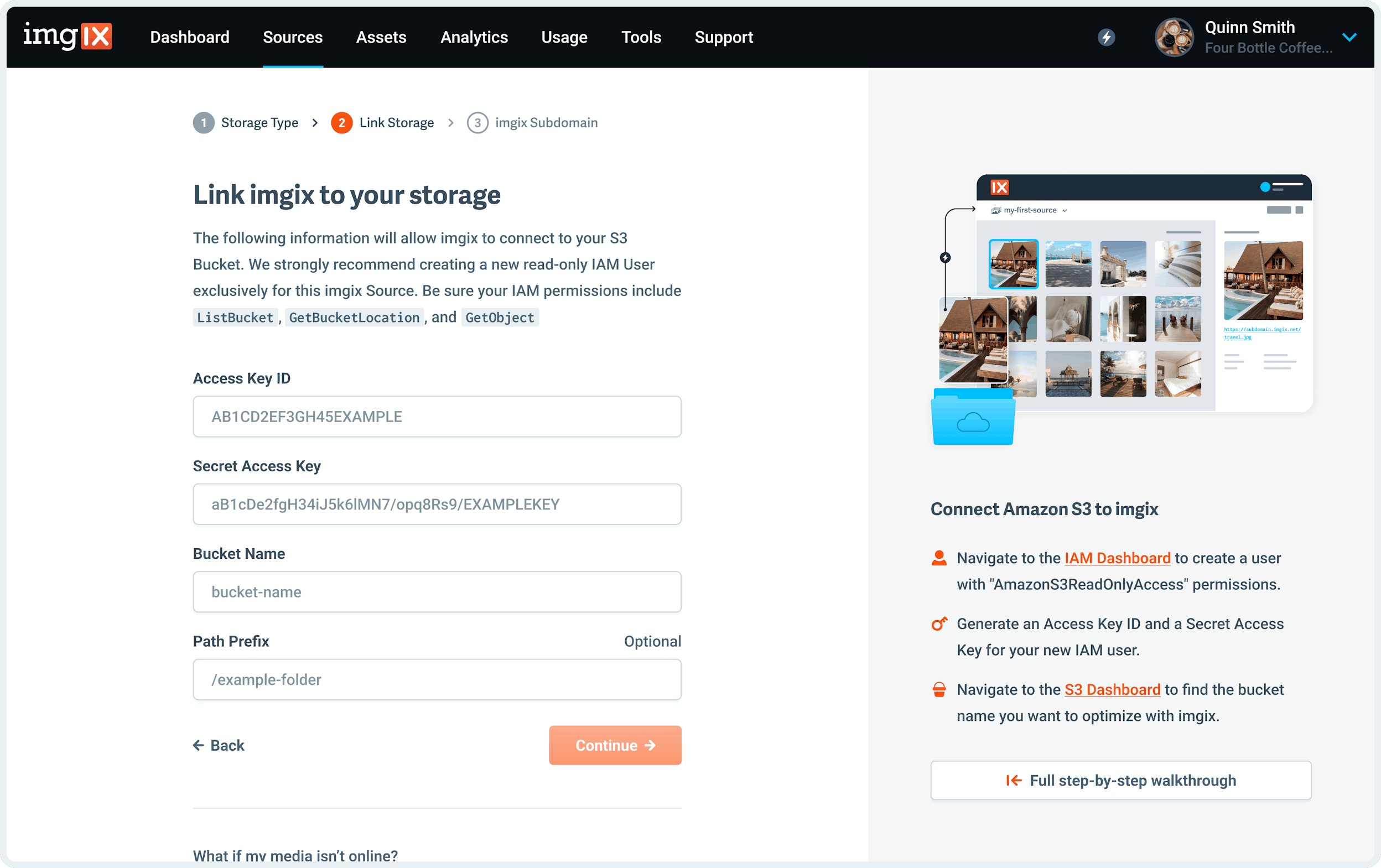
Note: We strongly recommend creating an Amazon IAM account specifically for Imgix to access your S3 bucket with. Keep in mind that Imgix only requires
ReadandListpermissions to begin serving your assets. For more information on permissions, how to generate your Access Key and Secret Access Keys, or where to find your Bucket Name see the Amazon S3 Guide and Security documentation.- Access Key ID: The access key of the
deployment credentialsyou want Imgix to connect with. - Secret Access Key: The secret key of the
deployment credentialsyou want Imgix to connect with. - Bucket Name: The name of the bucket containing the assets you want Imgix to connect to.
- Path Prefix (optional): The folder prefix you want to resolve to (if it exists). The prefix is prepended to the asset path before resolving the asset in S3. By default the asset path is
/.
- Access Key ID: The access key of the
-
Name the Subdomain you’d like to use as the base URL for your assets.
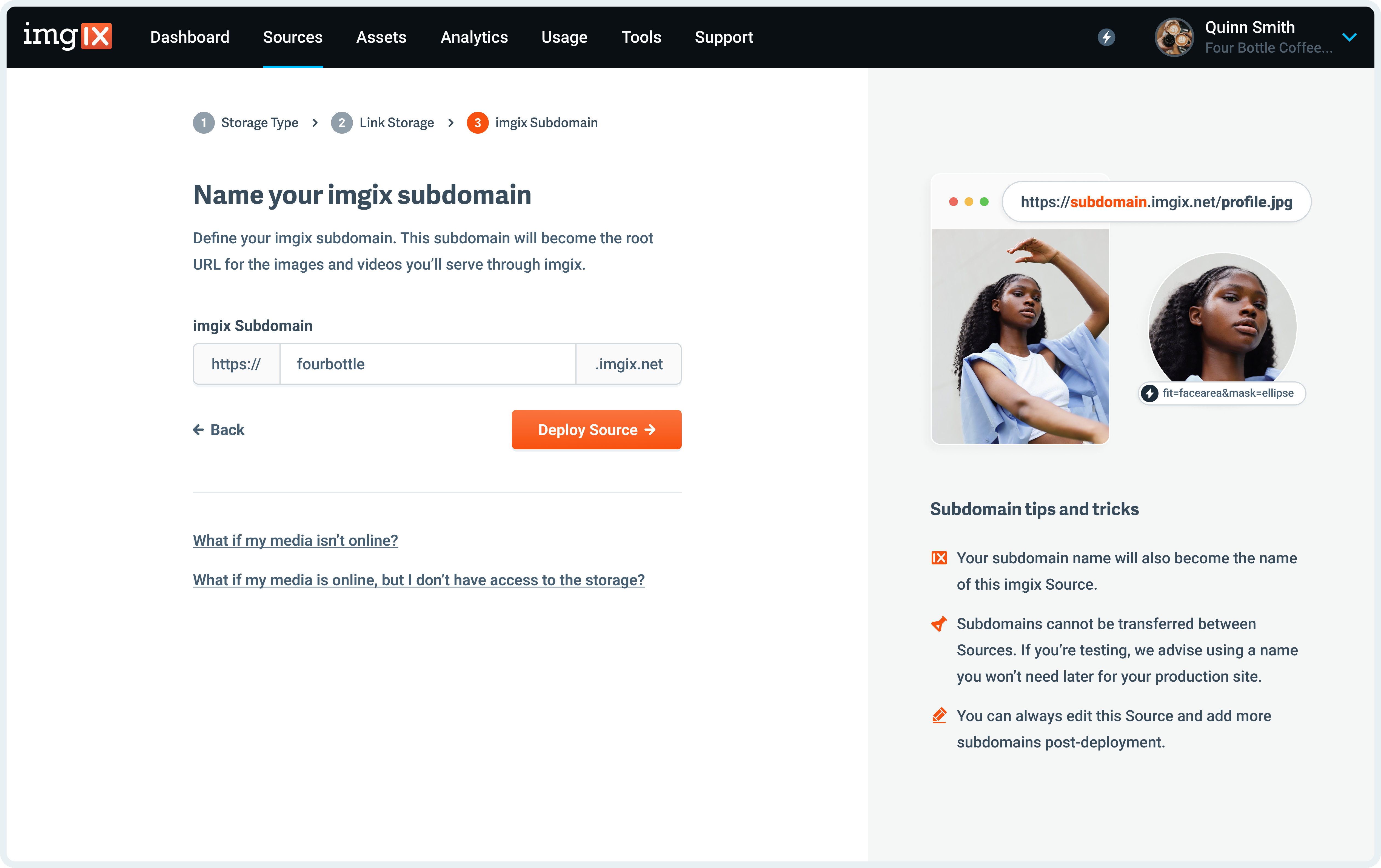
Note: The subdomain name you choose is unique to your Source and can’t be re-used. If you’re setting up a Source with a lot of customization (particularly a Custom Domain), choose the name you plan to use going forward.
- Click the Deploy Source button on Step #3 to queue your Source for deployment.
Amazon S3 Guide and Security
We strongly recommend creating an Amazon IAM user specifically for Imgix to access your S3 bucket with. All Amazon credentials are stored using industry standard cryptographic best practices.
IAM users help businesses maintain security by only granting specific individuals or, in our case, a specific application access to their S3 buckets. Imgix only requires read permissions to connect to your bucket and begin serving your media.
Advanced Policy Template
Imgix only needs a few read-only permissions to properly fetch assets. To add an additional layer of security, use a limited-permissions IAM user that is only used for Imgix and only for the bucket containing your assets.
The specific S3 permissions Imgix requires are:
ListBucketGetBucketLocationGetObject
Advanced Policy Example
{
"Statement": [
{
"Effect": "Allow",
"Action": ["s3:GetObject", "s3:ListBucket", "s3:GetBucketLocation"],
"Resource": ["arn:aws:s3:::your-bucket/*", "arn:aws:s3:::your-bucket"]
}
]
}Note: If you decide to manually build your policy, please double-check it with the Amazon IAM Policy Simulator.
Advanced Settings
See the Advanced Source Settings for information about setting up custom domains, defaults, and cache TTL options.
Uploading
You must follow additional steps to configure your Source to upload assets directly to Amazon S3. See the Uploading to Amazon S3 documentation for more information.